When you manage infrastructure inside a customer's VPC, you are not just delivering code. You are managing a living environment that belongs to someone else.
The biggest hurdle to scaling BYOC is not the code. It's the anxiety. It's the fear that a minor configuration change will accidentally expose a database or trigger runaway cloud costs that undermine the trust you have built with your customer.
Nuon Policies turns your internal delivery standards into an enforceable contract between your application and your customer's cloud.
Why Code Review Is Not Enough
In a traditional SaaS model, code review is your primary gate. You assume that if the code is right, the environment is right. In a Bring Your Own Cloud (BYOC) world, that logic breaks down completely.
Code review catches intent, but it cannot catch environmental context. Imagine you are shipping a single update to hundreds of customers.
- Customer A has a strictly private VPC with no internet egress.
- Customer B allows public endpoints for specific integrations.
A Pull Request might pass code review and look perfect in your staging environment. However, when you deploy to every individual customer, that same code might trigger a security violation for Customer A while passing for Customer B.
While we use policies in standard SaaS to maintain internal standards, they are an absolute requirement for BYOC. You are not just testing once in a controlled staging area; you are essentially testing and verifying the configuration in each unique customer environment simultaneously.
By shifting policy enforcement left with Nuon, you are not just checking the code. You are checking the code against the specific, live reality of every individual customer install before a single resource is provisioned. This ensures that a global update does not create a local security crisis.
The "Day 30" Challenge: Detecting Environmental Drift
A successful deployment is only the starting point. In a customer-managed VPC, the environment is dynamic. Changes often happen outside of your control that can impact your application's compliance with customer requirements.
Consider a common scenario:
- The Deployment: Your team deploys an update. Nuon verifies that your database is isolated and the load balancer is internal-only. The policy passes, and the install is healthy.
- The Customer Change: Two weeks later, the customer's platform team modifies a shared VPC subnet or updates a global security group to accommodate a third-party tool.
- The Violation: This change unintentionally exposes your application's internal endpoints or alters the network boundary.
Because your code did not change, a standard CI/CD pipeline would never catch this. Your application is now running in a state that violates your security contract.
Nuon Policies solve this through Continuous Enforcement. By running Drift Scans on a schedule, Nuon compares the live state of the deployed infrastructure against your defined policies. When a customer change causes a violation, Nuon generates an alert immediately in addition to the Policy Report that's created every time a policy is evaluated.
Enforcing the Contract at the Gate
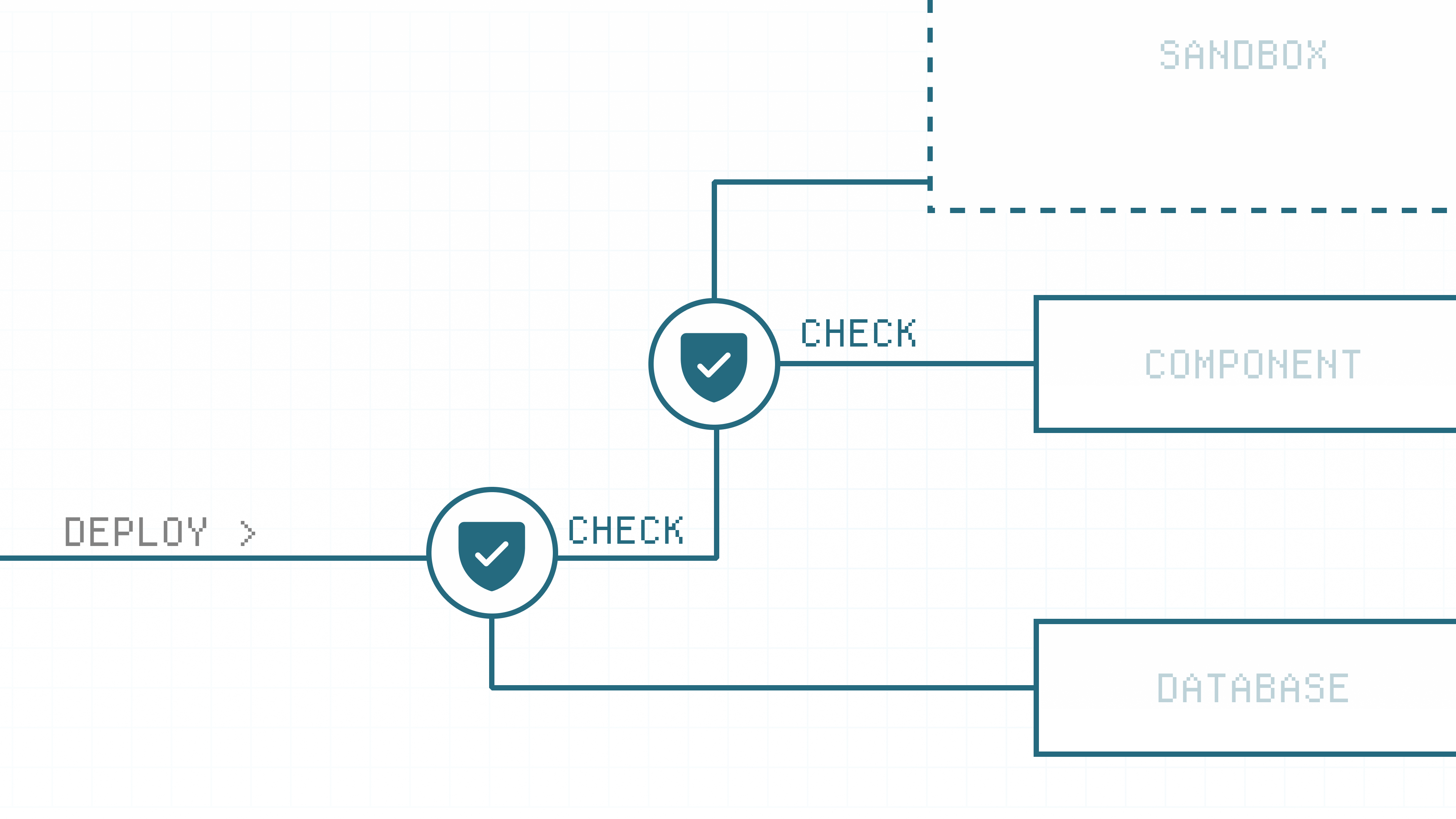
In modern infrastructure-as-code (IaC) workflows, we rely on a two-step cycle: Plan and Apply. The "Plan" is a deterministic calculation where the engine compares your desired state against the live environment. It shows you exactly which resources will be created, modified, or destroyed.
In a standard SaaS environment, you review this plan to ensure you are not about to delete a production database. In a BYOC world, this preview becomes even more critical. You are not just reviewing your own infrastructure; you are reviewing a proposed change against a customer's unique requirements.
By injecting Nuon Policies directly into this Plan phase, we create an automated validation gate. The policy engine inspects the calculated plan before the Apply step ever begins.
This turns the "Approve" button into a high-confidence action:
- Automatic Gating: If a change violates a Deny rule (such as an unencrypted volume or a public ALB), the deployment is blocked during the plan phase.
- Contextual Warnings: If a change triggers a Warn rule, the reviewer sees the specific policy context immediately.
Instead of discovering a security violation or an architectural mismatch after a deployment is already live in a customer's account, your team identifies the conflict at the exact moment the change is being proposed. This evaluation creates a permanent Policy Report, documenting the check regardless of the outcome.
More Use Cases: Codifying the Contract
Building on these per-plan checks, the Nuon control plane allows you to orchestrate these standards across your entire fleet of installs. As a vendor, this gives you the confidence that a single global change remains compliant for every customer, regardless of their unique environment.
By leveraging OPA and Rego, you can codify the specific "asks" of your customer's security and platform teams into automated guardrails. Here are the most common ways our partners use the Policy Catalog to manage their installs:
Security & Integrity: Software Transparency
Example: Requiring signed images and SBOMs at build time.
Enterprise customers need to know exactly what is running in their cloud. By enforcing these requirements during the build and plan phases, you automate a core part of the security audit. You ensure every artifact is verified and traceable before it ever leaves your pipeline.
Infrastructure Safety: Resource Discipline
Example: Restricting instance sizes or storage types.
Managing infrastructure in someone else's cloud requires strict cost control. These policies prevent unmanaged cost spikes by ensuring your application stays within the technical and financial boundaries agreed upon with the customer.
VPC Locality: Data Residency Guardrails
Example: Ensuring all traffic and data flow stay within the designated VPC.
For many, the primary reason for BYOC is data residency. You can codify network rules that provide automated proof that sensitive data never leaves the customer's controlled environment. This turns a complex compliance requirement into a simple, green checkmark on a policy report.
We are building a policy examples with use cases we have seen. And, sign up for a Nuon account , and you can deploy an example app with policies .
From Enforcement to Continuous Auditing
In the world of enterprise software, policies are not just about stopping bad changes. They are about providing continuous proof of compliance.
Every time Nuon evaluates a policy, whether during a proactive deployment plan or a reactive drift scan, it generates a Policy Report. These reports provide a detailed audit trail of what was checked, who defined the rule, and the specific result.
For your customers, these reports are the bridge to trust. Instead of a manual quarterly audit, you can provide an automated, real-time record showing that every change to their environment met their security and operational standards. It turns the report from a simple failure notification into a continuous ledger of compliance.
Standard CI/CD is built to move bits to your own infrastructure. Nuon is built to manage a contract inside someone else's.
By unifying approvals, drift, and policies into a single control plane, we have replaced fragile, home-grown scripts with the deterministic governance required to scale BYOC.
Ready to get started?
Deploy your application into customer clouds
See how Nuon can help you unlock BYOC deployment for your entire customer base.
